Blocking Insider Threats and Developing an Organizations Security Culture
Blocking Insider Threats and Developing an Organizations’ Security Culture
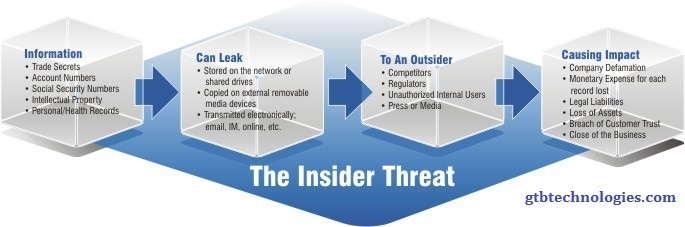
The risk to companies posed by the insider threat, presents a unique challenge to company IT security.
According to recent research, the danger of the insider may very well be the single biggest threat facing organizations today, accounting for as much as 75 percent of all breaches over the recent period. It is not surprising that in a 2017 survey of US government workers, all employees questioned suspected a colleague of being responsible when a breach occurred.
The Delicate Balance
The insider threat companies have to account for is not limited to malicious actors betraying an organization’s system. Rather, it includes the full range of compromising actions often taken by employees that make the company’s system vulnerable to attack or otherwise expose sensitive data. These actions are often taken completely unintentionally.
From downloading dangers files from a phishing scam, to moving sensitive files out of their secure location on a network, the range of harmful actions that are regularly taken by employees is wide.
Combating the insider threat has often meant companies shooting themselves in the leg. Placing blanket restrictions on data access and transfer impedes the workflow of an organization. Additionally, while set security protocols are important, they fail to address the dynamic nature of network data. The definitions of what constitutes sensitive information often changes depending on time, context, and the specific task at hand.
The Smart Solution
Preventing inside actors from exposing an organization from within requires an effective security culture, not just pre-determined network rules. Data protocols cannot be a set-it-and-forget-it thing. The proper handling of information is a process that has to be constantly reviewed and adjusted and re-instilled into the ever-changing work environment. Placing that responsibility on human security officers and analysts can be overburdening, as well as inefficient.
Eliminate Insider Threats – Accurately!
GTB’s Data Loss solution applies smart algorithms to the monitoring of data activity. Content-aware programs categorize outbound and inbound data transmissions from a company network, all in real-time. The detection algorithms “understand” the data flow of a system in order to accurately detect important data streams. This ensures that potentially compromising actions taken within the network, from careless exposure of files to malicious attempts to expose sensitive data from within, do not go unnoticed by security managers. GTB identifies and eliminates insider threats with real-time detection, control, and prevention of sensitive data exfiltration, including threats from malicious insiders and malware-based data exfiltration. Using logs from many on-premises and cloud services, an organization can create GTB policies that monitor for risk signals, such as policy infractions, then take remediation actions such as initiating an investigation or educating end-users.
Intelligent Data Loss Prevention (DLP), helps companies achieve the secure culture they need to handle their data over time by educating end-users while enhancing their knowledge of and compliance with organization governance policies. Only an intelligent DLP platform can bring about an effective security framework while avoiding hindering an organization’s operations, and maintaining seamless workflows.
